| Name: | macOS Big Sur 11.2.2 (20D80)_Site.com.dmg |
|---|---|
| Size: | 11.38 GB |
| Files | macOS Big Sur 11.2.2 (20D80)_Site.com.dmg [11.38 GB] |
macOS Big Sur 11.2.2 (20D80) Multilingual
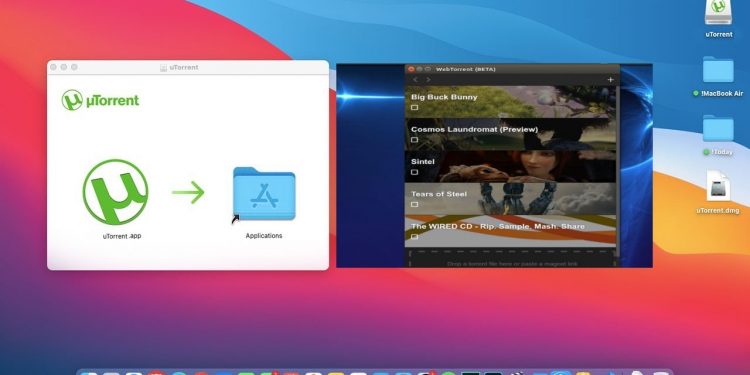
July 8, 2021: Apple releases macOS Big Sur 11.5 beta 5 for developers. The fifth beta of macOS Big Sur 11.5 is now available for developers. Follow the instructions below to get started with the macOS Big Sur beta. If you've been waiting for macOS Big Sur to start testing with macOS, now's the time to start downloading. Utorrent Mac Os Big Sur. MacOS Big Sur is the latest operating system release for the Mac, and introduces many new features to make your Mac experience more optimized and refined than ever before. In this article, we’re going to cover six major changes made to Big Sur and more importantly, we will provide download macOS Big Sur Torrent Image. Utorrent Pour Mac Os Big Sur Mac Os X Big Sur Download A new macOS that welcomes the arrival of Apple Silicon and offers better integration with mobile platforms, along with fresh visuals and a host of other features. Big Sur represents a major redesign of Apple's macOS, appropriately marked by the first major version number change in 20 years; yes, we're finally on macOS 11.0. This update coincides with the release of Apple's very first in-house ARM-based SoC for Macs, and we can see why. Big Sur support is, as of now, is still under experiment. Visit: qbittorrent. Comparatively, this torrent downloader is fairly lightweight and is accompanied by a smaller installer. The torrent you wish to obtain can be looked for right from within the app itself. Plus, the downloads can be prioritized too.
macOS Big Sur elevates the world’s most advanced desktop operating system to a new level of power and beauty. Experience Mac to the fullest with a refined new design. Enjoy the biggest Safari update ever. Discover new features for Maps and Messages. And get even more transparency around your privacy.
Design
- New design for apps makes it easier to focus on your content and take action with space efficient toolbars and full height sidebars
- Updated menu bar features wider spacing and a new translucent material that becomes more vibrant when you interact with it
- Refreshed system sounds include the boot chime and sounds for transferring files, moving items to the trash, locking files, and more
Control Center
- Control Center puts your favorite menus and controls in one handy place in the menu bar so you can quickly adjust settings as you work
- Additional controls appear when you click to expand Control Center menus
- Support for pinning favorite menus from Control Center to the menu bar
Notification Center
- Updated Notification Center brings notifications and widgets together in one view
- Interactive notifications display additional actions you can take with a deep press
- Beautiful, new data-rich widgets for Calendar, Clock, Notes, Photos, Podcasts, Reminders, Screen Time, Stocks, and Weather
- Edit view lets you to add new widgets and customize their size
- Support for widgets from third-party apps
Safari
- World’s fastest desktop browser with industry-leading performance and energy efficiency*
- Customizable new start page lets you set a background image and decide what appears, including Reading List, iCloud Tabs, Privacy Report and more
- Expanded extensions support and new dedicated category in the App Store for discovering new extensions
- New tab design featuring favicons in tabs, and website previews that appear when you hover over a tab
- Translation (beta) for English, Spanish, Simplified Chinese, French, German, Russian or Brazilian Portuguese
- Privacy Report gives you visibility into how Safari keeps your browsing your business, with an overview of trackers blocked by Intelligent Tracking Prevention
- Safari password monitoring securely screens saved passwords for any that may have been involved in a data breach
- Safari privacy prompts for extensions let you choose when a website can work with an extension
Messages
Pinned conversations keep up to nine of your favorite threads at the top of the list
- Mentions let you direct a message to an individual in a group conversation
- Inline replies let you reply to a specific message earlier in the conversation
- Message effects for balloons, confetti, lasers and more
- #images helps you find and add trending GIFs to messages
- Memoji makes it simple to create a personalized character and send stickers that match your mood and personality
Maps
- Guides offer recommendations for places to go and things to do, curated by a selection of trusted brands
- Look Around to explore cities in a high-resolution, interactive 3D experience
- Indoor maps for major airports and shopping centers
- Cycling directions helps you find bike-friendly routes to your destination
- Electric vehicle routing helps you plan trips for supported vehicles that you add on iPhone
Big Sur compatible Macs:
- MacBook 2015 and later
- MacBook Air 2013 and later
- MacBook Pro Late 2013 and later
- Mac mini 2014 and later
- iMac 2014 and later
- iMac Pro 2017 and later
- Mac Pro 2013 and later
What’s New:
Version 11.2.2
- macOS Big Sur 11.2.2 prevents MacBook Pro (2019 or later) and MacBook Air (2020 or later) models from incurring damage when they are connected to certain third-party, non-compliant powered USB-C hubs and docks.
Version 11.2
macOS Big Sur 11.2 improves Bluetooth reliability and fixes the following issues:
- External displays may show a black screen when connected to a Mac mini (M1, 2020) using an HDMI to DVI converter
- Edits to Apple ProRAW photos in the Photos app may not save
- iCloud Drive could turn off after disabling the iCloud Drive Desktop & Documents Folders option
- System Preferences may not unlock when entering your administrator password
- Globe key may not display the Emoji & Symbols pane when pressed
Compatibility: OS X 10.9 or later, 64-bit processor
Homepagehttps://www.apple.com/macos/big-sur/
About Apple security updates
For our customers' protection, Apple doesn't disclose, discuss, or confirm security issues until an investigation has occurred and patches or releases are available. Recent releases are listed on the Apple security updates page.
Apple security documents reference vulnerabilities by CVE-ID when possible.
For more information about security, see the Apple Product Security page.
macOS Big Sur 11.4
Released May 24, 2021
AMD
Available for: macOS Big Sur
Impact: A remote attacker may be able to cause unexpected application termination or arbitrary code execution
Description: A logic issue was addressed with improved state management.
CVE-2021-30678: Yu Wang of Didi Research America
AMD
Available for: macOS Big Sur
Impact: A local user may be able to cause unexpected system termination or read kernel memory
Description: A logic issue was addressed with improved state management.
CVE-2021-30676: shrek_wzw
App Store
Available for: macOS Big Sur
Impact: A malicious application may be able to break out of its sandbox
Description: A path handling issue was addressed with improved validation.
CVE-2021-30688: Thijs Alkemade of Computest Research Division
AppleScript
Available for: macOS Big Sur
Impact: A malicious application may bypass Gatekeeper checks
Description: A logic issue was addressed with improved state management.
CVE-2021-30669: Yair Hoffman
Audio
Available for: macOS Big Sur
Impact: Processing a maliciously crafted audio file may lead to arbitrary code execution
Description: This issue was addressed with improved checks.
CVE-2021-30707: hjy79425575 working with Trend Micro Zero Day Initiative
Audio
Available for: macOS Big Sur
Impact: Parsing a maliciously crafted audio file may lead to disclosure of user information
Description: This issue was addressed with improved checks.
CVE-2021-30685: Mickey Jin (@patch1t) of Trend Micro
Bluetooth
Available for: macOS Big Sur
Impact: A memory corruption issue was addressed with improved state management
Description: A malicious application may be able to gain root privileges
CVE-2021-30672: say2 of ENKI
Entry added July 21, 2021
Core Services
Available for: macOS Big Sur
Impact: A malicious application may be able to gain root privileges
Description: A validation issue existed in the handling of symlinks. This issue was addressed with improved validation of symlinks.
CVE-2021-30681: Zhongcheng Li (CK01)
CoreAudio
Available for: macOS Big Sur
Impact: Processing a maliciously crafted audio file may disclose restricted memory
Description: An out-of-bounds read was addressed with improved bounds checking.
CVE-2021-30686: Mickey Jin of Trend Micro
CoreText
Available for: macOS Big Sur
Impact: An out-of-bounds read was addressed with improved input validation
Description: Processing a maliciously crafted font may result in the disclosure of process memory.
CVE-2021-30733: Sunglin from the Knownsec 404
CVE-2021-30753: Xingwei Lin of Ant Security Light-Year Lab
Entry added July 21, 2021
Crash Reporter
Available for: macOS Big Sur
Impact: A malicious application may be able to modify protected parts of the file system
Description: A logic issue was addressed with improved state management.
CVE-2021-30727: Cees Elzinga
CVMS
Available for: macOS Big Sur
Impact: A local attacker may be able to elevate their privileges
Description: This issue was addressed with improved checks.
CVE-2021-30724: Mickey Jin (@patch1t) of Trend Micro
Dock
Available for: macOS Big Sur
Impact: A malicious application may be able to access a user's call history
Description: An access issue was addressed with improved access restrictions.
CVE-2021-30673: Josh Parnham (@joshparnham)
FontParser
Available for: macOS Big Sur
Impact: An out-of-bounds read was addressed with improved input validation
Description: Processing a maliciously crafted font may result in the disclosure of process memory
CVE-2021-30755: Xingwei Lin of Ant Security Light-Year Lab
Entry added July 21, 2021
Graphics Drivers
Available for: macOS Big Sur
Impact: A remote attacker may cause an unexpected application termination or arbitrary code execution
Description: A logic issue was addressed with improved state management.
CVE-2021-30684: Liu Long of Ant Security Light-Year Lab
Graphics Drivers
Available for: macOS Big Sur
Impact: A malicious application may be able to execute arbitrary code with kernel privileges
Description: An out-of-bounds write issue was addressed with improved bounds checking.
CVE-2021-30735: Jack Dates of RET2 Systems, Inc. (@ret2systems) working with Trend Micro Zero Day Initiative
Heimdal
Available for: macOS Big Sur
Impact: A local user may be able to leak sensitive user information
Description: A logic issue was addressed with improved state management.
CVE-2021-30697: Gabe Kirkpatrick (@gabe_k)
Heimdal
Available for: macOS Big Sur
Impact: A malicious application may cause a denial of service or potentially disclose memory contents
Description: A memory corruption issue was addressed with improved state management.
CVE-2021-30710: Gabe Kirkpatrick (@gabe_k)
Heimdal
Available for: macOS Big Sur
Impact: A malicious application could execute arbitrary code leading to compromise of user information
Description: A use after free issue was addressed with improved memory management.
CVE-2021-30683: Gabe Kirkpatrick (@gabe_k)
ImageIO
Available for: macOS Big Sur
Impact: Processing a maliciously crafted image may lead to disclosure of user information
Description: An out-of-bounds read was addressed with improved bounds checking.
CVE-2021-30687: Hou JingYi (@hjy79425575) of Qihoo 360
ImageIO
Available for: macOS Big Sur
Impact: Processing a maliciously crafted image may lead to disclosure of user information
Description: This issue was addressed with improved checks.
CVE-2021-30700: Ye Zhang(@co0py_Cat) of Baidu Security
ImageIO
Available for: macOS Big Sur
Impact: Processing a maliciously crafted image may lead to arbitrary code execution
Description: This issue was addressed with improved checks.
CVE-2021-30701: Mickey Jin (@patch1t) of Trend Micro and Ye Zhang of Baidu Security
ImageIO
Available for: macOS Big Sur
Impact: Processing a maliciously crafted ASTC file may disclose memory contents
Description: This issue was addressed with improved checks.
CVE-2021-30705: Ye Zhang of Baidu Security
ImageIO
Available for: macOS Big Sur
Impact: This issue was addressed with improved checks
Description: Processing a maliciously crafted image may lead to disclosure of user information.
CVE-2021-30706: Anonymous working with Trend Micro Zero Day Initiative, Jzhu working with Trend Micro Zero Day Initiative
Entry added July 21, 2021
Intel Graphics Driver
Available for: macOS Big Sur
Impact: A local user may be able to cause unexpected system termination or read kernel memory
Description: An out-of-bounds read issue was addressed by removing the vulnerable code.
CVE-2021-30719: an anonymous researcher working with Trend Micro Zero Day Initiative
Intel Graphics Driver
Available for: macOS Big Sur
Impact: A malicious application may be able to execute arbitrary code with kernel privileges
Description: An out-of-bounds write issue was addressed with improved bounds checking.
CVE-2021-30728: Liu Long of Ant Security Light-Year Lab
CVE-2021-30726: Yinyi Wu(@3ndy1) of Qihoo 360 Vulcan Team
IOUSBHostFamily
Available for: macOS Big Sur
Impact: This issue was addressed with improved checks
Description: An unprivileged application may be able to capture USB devices.
CVE-2021-30731: UTM (@UTMapp)
Entry added July 21, 2021
Kernel
Available for: macOS Big Sur
Impact: A malicious application may be able to execute arbitrary code with kernel privileges
Description: A logic issue was addressed with improved validation.
CVE-2021-30740: Linus Henze (pinauten.de)
Kernel
Available for: macOS Big Sur
Download Torrents For Mac
Impact: An application may be able to execute arbitrary code with kernel privileges
Description: A logic issue was addressed with improved state management.
CVE-2021-30704: an anonymous researcher
Kernel
Available for: macOS Big Sur
Impact: Processing a maliciously crafted message may lead to a denial of service
Description: A logic issue was addressed with improved state management.
CVE-2021-30715: The UK's National Cyber Security Centre (NCSC)
Kernel
Available for: macOS Big Sur
Impact: An application may be able to execute arbitrary code with kernel privileges
Description: A buffer overflow was addressed with improved size validation.
CVE-2021-30736: Ian Beer of Google Project Zero
Kernel
Available for: macOS Big Sur
Impact: A local attacker may be able to elevate their privileges
Description: A memory corruption issue was addressed with improved validation.
CVE-2021-30739: Zuozhi Fan (@pattern_F_) of Ant Group Tianqiong Security Lab
Kernel
Available for: macOS Big Sur
Impact: A double free issue was addressed with improved memory management
Description: An application may be able to execute arbitrary code with kernel privileges.
CVE-2021-30703: an anonymous researcher
Entry added July 21, 2021
Kext Management
Available for: macOS Big Sur
Impact: A local user may be able to load unsigned kernel extensions
Description: A logic issue was addressed with improved state management.
CVE-2021-30680: Csaba Fitzl (@theevilbit) of Offensive Security
LaunchServices
Available for: macOS Big Sur
Impact: A malicious application may be able to break out of its sandbox
Description: This issue was addressed with improved environment sanitization.
CVE-2021-30677: Ron Waisberg (@epsilan)
Login Window
Available for: macOS Big Sur
Impact: A person with physical access to a Mac may be able to bypass Login Window
Description: A logic issue was addressed with improved state management.
CVE-2021-30702: Jewel Lambert of Original Spin, LLC.
Available for: macOS Big Sur
Impact: An attacker in a privileged network position may be able to misrepresent application state
Description: A logic issue was addressed with improved state management.
CVE-2021-30696: Fabian Ising and Damian Poddebniak of Münster University of Applied Sciences
MediaRemote
Available for: macOS Big Sur
Impact: A privacy issue in Now Playing was addressed with improved permissions
Description: A local attacker may be able to view Now Playing information from the lock screen.
CVE-2021-30756: Ricky D'Amelio, Jatayu Holznagel (@jholznagel)
Entry added July 21, 2021
Model I/O
Available for: macOS Big Sur
Impact: Processing a maliciously crafted USD file may disclose memory contents
Description: An information disclosure issue was addressed with improved state management.
CVE-2021-30723: Mickey Jin (@patch1t) of Trend Micro
CVE-2021-30691: Mickey Jin (@patch1t) of Trend Micro
CVE-2021-30692: Mickey Jin (@patch1t) of Trend Micro
CVE-2021-30694: Mickey Jin (@patch1t) of Trend Micro
Model I/O
Available for: macOS Big Sur
Impact: Processing a maliciously crafted USD file may lead to unexpected application termination or arbitrary code execution
Description: A memory corruption issue was addressed with improved state management.
CVE-2021-30725: Mickey Jin (@patch1t) of Trend Micro
Model I/O
Available for: macOS Big Sur
Impact: Processing a maliciously crafted USD file may disclose memory contents
Description: An out-of-bounds read was addressed with improved input validation.
CVE-2021-30746: Mickey Jin (@patch1t) of Trend Micro
Model I/O
Available for: macOS Big Sur
Impact: Processing a maliciously crafted image may lead to arbitrary code execution
Description: A validation issue was addressed with improved logic.
CVE-2021-30693: Mickey Jin (@patch1t) & Junzhi Lu (@pwn0rz) of Trend Micro
Model I/O
Available for: macOS Big Sur
Impact: Processing a maliciously crafted USD file may disclose memory contents
Description: An out-of-bounds read was addressed with improved bounds checking.
CVE-2021-30695: Mickey Jin (@patch1t) & Junzhi Lu (@pwn0rz) of Trend Micro
Model I/O
Available for: macOS Big Sur
Impact: Processing a maliciously crafted USD file may lead to unexpected application termination or arbitrary code execution
Description: An out-of-bounds read was addressed with improved input validation.
CVE-2021-30708: Mickey Jin (@patch1t) & Junzhi Lu (@pwn0rz) of Trend Micro
Model I/O
Available for: macOS Big Sur
Impact: Processing a maliciously crafted USD file may disclose memory contents
Description: This issue was addressed with improved checks.
CVE-2021-30709: Mickey Jin (@patch1t) of Trend Micro

NSOpenPanel
Available for: macOS Big Sur
Impact: An application may be able to gain elevated privileges
Description: This issue was addressed by removing the vulnerable code.
CVE-2021-30679: Gabe Kirkpatrick (@gabe_k)
OpenLDAP
Available for: macOS Big Sur
Impact: A remote attacker may be able to cause a denial of service
Description: This issue was addressed with improved checks.
CVE-2020-36226
CVE-2020-36227
CVE-2020-36223
CVE-2020-36224
CVE-2020-36225
CVE-2020-36221
CVE-2020-36228
CVE-2020-36222
CVE-2020-36230
CVE-2020-36229
PackageKit
Available for: macOS Big Sur
Impact: A malicious application may be able to overwrite arbitrary files
Description: An issue with path validation logic for hardlinks was addressed with improved path sanitization.
CVE-2021-30738: Qingyang Chen of Topsec Alpha Team and Csaba Fitzl (@theevilbit) of Offensive Security
Sandbox
Available for: macOS Big Sur
Impact: A malicious application may be able to bypass certain Privacy preferences
Description: This issue was addressed with improved data protection.
CVE-2021-30751: Csaba Fitzl (@theevilbit) of Offensive Security
Entry added July 21, 2021
Security
Available for: macOS Big Sur
Impact: Processing a maliciously crafted certificate may lead to arbitrary code execution
Description: A memory corruption issue in the ASN.1 decoder was addressed by removing the vulnerable code.
CVE-2021-30737: xerub
smbx
Available for: macOS Big Sur
Impact: An attacker in a privileged network position may be able to perform denial of service
Description: A logic issue was addressed with improved state management.
CVE-2021-30716: Aleksandar Nikolic of Cisco Talos
smbx
Available for: macOS Big Sur
Impact: An attacker in a privileged network position may be able to execute arbitrary code
Description: A memory corruption issue was addressed with improved state management.
CVE-2021-30717: Aleksandar Nikolic of Cisco Talos

smbx
Available for: macOS Big Sur
Impact: An attacker in a privileged network position may be able to leak sensitive user information
Description: A path handling issue was addressed with improved validation.
CVE-2021-30721: Aleksandar Nikolic of Cisco Talos
smbx
Available for: macOS Big Sur
Impact: An attacker in a privileged network position may be able to leak sensitive user information
Description: An information disclosure issue was addressed with improved state management.
CVE-2021-30722: Aleksandar Nikolic of Cisco Talos
smbx
Available for: macOS Big Sur
Impact: A remote attacker may be able to cause unexpected application termination or arbitrary code execution
Description: A logic issue was addressed with improved state management.
CVE-2021-30712: Aleksandar Nikolic of Cisco Talos
Software Update
Available for: macOS Big Sur
Impact: A person with physical access to a Mac may be able to bypass Login Window during a software update
Description: This issue was addressed with improved checks.
CVE-2021-30668: Syrus Kimiagar and Danilo Paffi Monteiro
SoftwareUpdate
Available for: macOS Big Sur
Impact: A non-privileged user may be able to modify restricted settings
Description: This issue was addressed with improved checks.
CVE-2021-30718: SiQian Wei of ByteDance Security
TCC
Macos Big Sur Torrent Download
Available for: macOS Big Sur
Impact: A malicious application may be able to send unauthorized Apple events to Finder
Description: A validation issue was addressed with improved logic.
CVE-2021-30671: Ryan Bell (@iRyanBell)
TCC
Available for: macOS Big Sur
Impact: A malicious application may be able to bypass Privacy preferences. Apple is aware of a report that this issue may have been actively exploited.
Description: A permissions issue was addressed with improved validation.
CVE-2021-30713: an anonymous researcher
WebKit
Available for: macOS Big Sur
Impact: Processing maliciously crafted web content may lead to universal cross site scripting
Description: A cross-origin issue with iframe elements was addressed with improved tracking of security origins.
CVE-2021-30744: Dan Hite of jsontop
WebKit
Available for: macOS Big Sur
Impact: Processing maliciously crafted web content may lead to arbitrary code execution
Description: A use after free issue was addressed with improved memory management.
CVE-2021-21779: Marcin Towalski of Cisco Talos
WebKit
Available for: macOS Big Sur
Impact: A malicious application may be able to leak sensitive user information
Description: A logic issue was addressed with improved restrictions.
CVE-2021-30682: Prakash (@1lastBr3ath)
Entry updated July 21, 2021
WebKit
Available for: macOS Big Sur
Impact: Processing maliciously crafted web content may lead to universal cross site scripting
Description: A logic issue was addressed with improved state management.
CVE-2021-30689: an anonymous researcher
WebKit
Available for: macOS Big Sur
Impact: Processing maliciously crafted web content may lead to arbitrary code execution
Description: Multiple memory corruption issues were addressed with improved memory handling.
CVE-2021-30749: an anonymous researcher and mipu94 of SEFCOM lab, ASU. working with Trend Micro Zero Day Initiative
CVE-2021-30734: Jack Dates of RET2 Systems, Inc. (@ret2systems) working with Trend Micro Zero Day Initiative
WebKit
Available for: macOS Big Sur
Impact: A malicious website may be able to access restricted ports on arbitrary servers
Description: A logic issue was addressed with improved restrictions.
CVE-2021-30720: David Schütz (@xdavidhu)
WebRTC
Available for: macOS Big Sur
Impact: A remote attacker may be able to cause a denial of service
Description: A null pointer dereference was addressed with improved input validation.
CVE-2021-23841: Tavis Ormandy of Google
CVE-2021-30698: Tavis Ormandy of Google
Additional recognition
App Store
We would like to acknowledge Thijs Alkemade of Computest Research Division for their assistance.
CoreCapture
We would like to acknowledge Zuozhi Fan (@pattern_F_) of Ant-financial TianQiong Security Lab for their assistance.
ImageIO
We would like to acknowledge Jzhu working with Trend Micro Zero Day Initiative and an anonymous researcher for their assistance.
Mail Drafts
We would like to acknowledge Lauritz Holtmann (@_lauritz_) for their assistance.
WebKit
We would like to acknowledge Chris Salls (@salls) of Makai Security for their assistance.